Sunday, December 10, 2017
It's Amazon vs. Google. Did You Know?
Have you ever or are you sometimes watching a YouTube video or two?
Have you ever or are you sometimes looking at something or even buying something on Amazon?
If you can answer any of above questions with Yes then you should read this article.
It shows very clearly why I always say that, no matter what companies say, we, the paying customer, are a voiceless, powerless "necessary evil". They just don't give a hoot about us.
Their talk of "how important" their customers are and how they care for us and how important it is for them "to serve the customer" is nothing but marketing hullabaloo and all too often they just plainly lie to us.
Never the less, I will stick with my Amazon Prime account and I will keep using Google's services.
For now at least.
Stay safe.
Monday, December 4, 2017
Attention Everybody ...
... with an AT&T, SBC Global or a Yahoo email account:
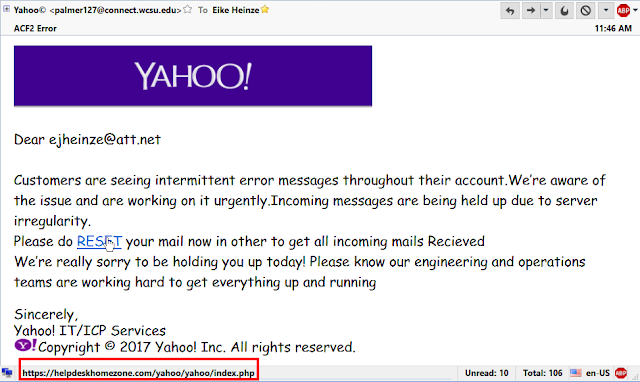
Likely every direct or indirect Yahoo user got this or an email similar to this:
DO NOT CLICK on the RESET link! This email is a scam!
As you can see my cursor was on the RESET link in the text when I took this screenshot.
Please look at the red framed box in the left bottom corner. You can easily see that the link would take you to helpdeskhomezone.com, a web site that obviously has NOTHING AT ALL to do with Yahoo! It is your guess what might happen if you do click on it.
Just the line where these crooks address me, "Dear ejkheinze@att.net" is another simple giveaway. No even vaguely reasonable company would address a customer like that!
Again, check every link in emails in this way BEFORE you click!
THINK TWICE and stay safe!
Likely every direct or indirect Yahoo user got this or an email similar to this:
DO NOT CLICK on the RESET link! This email is a scam!
As you can see my cursor was on the RESET link in the text when I took this screenshot.
Please look at the red framed box in the left bottom corner. You can easily see that the link would take you to helpdeskhomezone.com, a web site that obviously has NOTHING AT ALL to do with Yahoo! It is your guess what might happen if you do click on it.
Just the line where these crooks address me, "Dear ejkheinze@att.net" is another simple giveaway. No even vaguely reasonable company would address a customer like that!
Again, check every link in emails in this way BEFORE you click!
THINK TWICE and stay safe!
Friday, November 24, 2017
This is where I stand...
Despite being "only" a guest in the USA there have been quite a few times when I have been asked about my opinion of the so called "flag protest issue" in the NFL.
Here is a short video that gives my answer better than I ever could.
Happy Thanksgiving!
Monday, November 20, 2017
(GRAND-) PARENTS: Real and Present Danger!
Yes, I know, it has been way too long since the last time I had to say something.
With the holiday season immediately upon us and the crazy sales already in full swing:
You please, please have to read this article about the risks associated with the newfangled so-called "internet connected" toys.
Other than that I wish everybody a HAPPY THANKSGIVING!
Stay safe - and help keeping your kids and grand kids safe.
Monday, September 18, 2017
Why Me?
One time too many I have been asked by a caller why he should hire me rather than take his computer to Best Buy; here is my complete reply. I apologize for the bad style (way too many paragraphs begin with "I"!) but I am not a native English speaker.
In general
In general
- my main interest is cleaning your computer of all viruses and malware and securing it and your web browser against getting infected again in the future
- I have over 25 years of experience with Windows PCs plus over 23 years of experience as a computer programmer and database dministrator
- I do not mince words but rather say it as I see it
- I can explain technically complex concepts in layman's terms
- I prefer real-life usability and experience over personal opinions and commercial “tests”
- I abhor industry shenanigans and trickery and warn my customers
- I work on Windows PCs only and do only house calls up to 30 miles from my residence. There is no extra charge to appear at your door and I charge no mileage fees.
I neither sell material goods nor any software;
I sell only my experience, my know-how and my time.
I sell only my experience, my know-how and my time.
I do not charge sales tax.
I have NO contractual ties to any product;
I do not get any kickbacks from any manufacturer, wholesaler or dealer, no matter where and what you eventually buy.
I do not get any kickbacks from any manufacturer, wholesaler or dealer, no matter where and what you eventually buy.
I have absolutely no hidden financial interest or other commercial bias; there is no added or hidden cost for the home user.
With two rare exceptions I use and install only freely available and functionally proven programs.
Even a proven alternative to Microsoft Office® is officially available free of charge.
Even a proven alternative to Microsoft Office® is officially available free of charge.
I have worked professionally as a programmer and database administrator
- with computers since July 1st 1964
- with Microsoft software on CP/M computers since 1977
- with PCs since February 1982
- with Microsoft Windows since version 3.1 in 1992
For 11 years I was once every month the “computer guru” on a call-in talk show on WTKM radio out of Hartford, WI.
If you are interested please send an email to ejhprivate*AT*gmail*DOT*com
I will reply and send you my brochure with more information as a .pdf file;
if you rather want a paper copy please give me in your email your name and address and I will send you a letter.
if you rather want a paper copy please give me in your email your name and address and I will send you a letter.
The information in the brochure should enable you to decide whether you want to hire me to repair and secure your computer.
Thank you for your interest.
Saturday, August 26, 2017
Email Scammers At It Again
And again the email scammers are at it again. Most likely I got this email (see below) because my email address is publicly available thanks to Yahoo having gotten hacked about 2.5 to 3 years ago. It took a lot of public pressure until Yahoo well over two years after the fact finally admitted to hack #1 and then to hack #2.
Disclaimer: Both articles I just linked to are to be read carefully because they were, partially at least, written by journalists that are not computer technicians and/or with sensationalist attitude. The facts of the matter are not in question though!
I have many, many customers with email addresses ending in @att.net or @sbcglobal.net". At least theoretically they all could be affected likewise.
If you think something along the lines of "... but he has an email address ending with @att.net, why is he concerned by Yahoo having been hacked ..."? Well. many years ago AT&T didn't want the hassle of running their own email servers so they subcontracted Yahoo to do the technical handling of the email accounts of all AT&T customers; that includes in Wisconsin email addresses ending with @sbcglobal.net and country wide many others.. Thus all AT&T customers could be affected.
I have checked on Have I Been Pwned and yes, my email address is in both big customer files that got stolen from Yahoo. That "pwned" by the way is pronounced as "owned" and that is what it means. In geek speak it expresses that your computer - or here my email address - is 'owned' by somebody else who can do with it as they please.
Luckily my password did not get exposed but after I learned of the hack I changed it anyway, just to stay on the safe side.
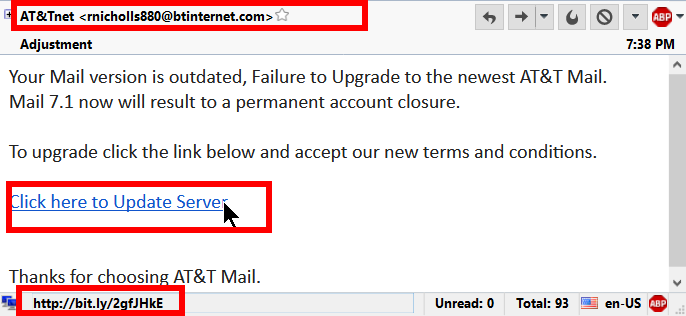
Now to the current reason why I write all this. I got this email:
- Sender Address: btinternet.com translates to BRITISH TELECOMMUNICATIONS PLC
NOTHING AT ALL to do with AT&T. - You see that I had my cursor on the "Click here..." link and
- because of the cursor on the link you can see in the left bottom corner of the email window the the link goes to bit.ly, a well know link shortening service.
Now THAT IS suspicious, for me at least.
Please, DO NOT be curious, DO NOT click on the link just because you want to see what happens; just delete the email and sleep in peace.
Stay safe!
Wednesday, July 26, 2017
How to Protect Yourself and Your Computer on the Internet
Sometimes I am still amazed by the degree of how clueless some people are as far as the most basic ways are concerned to stay safe on the Internet.
I don't want to repeat myself here and I don't want to sound like a broken record either. Oops, many younger readers would not even know what that means...
Anyway, here is a good and easy to read but admittedly fairly long article titled
Basic Computer Security: How to Protect Yourself from Viruses, Hackers, and Thieves
My regular readers will recognize that I quite often link to articles on How-To Geek. At least the articles about computers are an easy read and correct on top of it.
Stay safe.
Saturday, July 22, 2017
Why NOT TO USE Internet Explorer
About one to two times every month I encounter customers who react clearly with doubt or outright disbelief when I tell them NOT TO USE Internet Explorer. IE is Microsoft's web browser with roots in the mid 1990s. That is in computer terms ancient!
Finally I found an article on maketecheasier.com that explains the "why" in easily understandable terms. You find it here. Enjoy the read and please, please pass the word to your relatives and friends.
And if you are only a little bit like me you want to turn off IE totally. You find instructions on how to do that here.
Stay safe.
Friday, July 21, 2017
The Skinny ...
... about the latest outbreak of Encrypting Ransomware.
The original of this text was written by Ken Dwight, aka The Virus Doctor. I am an alumnus of his Virus Remediation Training and make this text available for my customers with his kind permission. Thanks Ken.
All my customers are advised to weekly initiate a check for Windows Updates. If they followed that advice their computers were protected and they don't need to care about these two overly "hyped up" virus outbreaks.
Stay safe.
The original of this text was written by Ken Dwight, aka The Virus Doctor. I am an alumnus of his Virus Remediation Training and make this text available for my customers with his kind permission. Thanks Ken.
As with malware in general, encrypting ransomware is continually changing. Most of these changes are evolutionary and somewhat predictable. As such, they don’t call for any significant changes in the methodology to be used in dealing with them.That was it.
Some recent developments in specific families and strains of encrypting ransomware are
significant enough to justify an update to the IT Support technician’s strategies and tactics for handling them effectively.
There are primarily two families of such ransomware that warrant this attention. Multiple names have been assigned to these families, but this discussion will use the names that are most frequently found in credible press coverage of these outbreaks.
WannaCry was released into the wild on May 12, 2017. According to most reports, it infected at least 200,000 computers, in more than 150 countries. This ransomware spawned its own Wikipedia entry, at
https://en.wikipedia.org/wiki/WannaCry_ransomware_attack.
The more recent attack, erroneously known as Petya, but more accurately referred to as
NotPetya, first struck on June 27, 2017. There are no estimates of the total number of computers infected by this malware, or the number of countries represented. But it clearly targeted businesses and organizations in Ukraine, with some 80% of the infections found there. This ransomware also has its own Wikipedia entry, at
https://en.wikipedia.org/wiki/2017_cyberattacks_on_Ukraine.
These two families of ransomware have several characteristics in common. Probably the most notable is the widespread coverage both received in the general press. While malware generally goes unreported in the non-trade press, these attacks were the exception to that rule. Fueling the press coverage was the revelation that both of these attacks were based on exploits developed by, and subsequently stolen from, the U. S. National Security Agency (NSA).
Interestingly enough, I have not seen any of these infections first-hand, nor have I received reports from any graduates of my Virus Remediation Training workshops that they have encountered computers encrypted by either of these families of ransomware. Considering the fact that hundreds of IT Support Techs fall into this category, in most of the United States + 7 foreign countries, I can only speculate that the actual infection rate is much less widespread than the press coverage would lead one to believe.
Another common denominator between these two infections was the fact that the vulnerability in Windows that was used for both of these attacks had been patched by Microsoft in their March, 2017 Windows Updates; any computer with that update applied would not have been infected by either of these pieces of malware.
Two NSA exploits were used in both of these attack scenarios; they are named EternalBlue and DoublePulsar. A free EternalBlue vulnerability scanner is available for download from http://omerez.com/eternal-blues-worldwide-statistics/. As of mid-July, 2017 more than 10 million IPs have been scanned; the majority of hosts scanned (53.82%) still have SMBv1 enabled, and 1 out of 9 hosts in a network is vulnerable to EternalBlue.
The WannaCry malware included a “Kill switch” which was discovered by a malware researcher and activated to disable the infection from spreading any further. No such kill switch has been found for NotPetya, but a “Vaccine” has been developed to protect against it. More details from Bleeping Computer at https://www.bleepingcomputer.com/news/security/vaccine-not-killswitch-found-for-petya-notpetya-ransomware-outbreak/.
Another important difference between these two families of malware involves the type of
encryption they perform on the victim’s hard drive. WannaCry, like most encrypting
ransomware, encrypts each individual file. It also changes the filename to end with an extension of .wcry.
On the other hand, NotPetya encrypts the entire hard drive and replaces the Master Boot Record with its own version. While the encryption is taking place, the malware displays a screen that looks like a chkdsk operation is being performed; when the whole-disk encryption is complete, it forces a reboot.
Upon the reboot, the modified MBR causes the ransom note to be displayed, with instructions to pay $300 USD in Bitcoin; after 72 hours, the ransom increases to $600 USD. Because of the modified MBR, at this point it is not possible to boot into a normal Windows environment.
As of this writing there is no means to pay the ransom; even if the ransom is paid, there appears to be no way to decrypt the hard drive or restore it to normal operation. Consequently, there is no reason to even consider paying the ransom.
Back to WannaCry, there have been some reports of successful decryption after paying the ransom. But here again, I have no first-hand (or even second-hand) reports from victims of this family of ransomware.
Those are the most recent, high-profile developments in the field of encrypting ransomware. But it’s a pretty safe bet they won’t be the last. This category of malware continues to evolve and become more sophisticated and more insidious. It has crossed the threshold of being a billion-dollar industry; that success will attract more and more criminals who are lured by the promise of easy money. Our prospects for future employment remain secure!
All my customers are advised to weekly initiate a check for Windows Updates. If they followed that advice their computers were protected and they don't need to care about these two overly "hyped up" virus outbreaks.
Stay safe.
Wednesday, May 10, 2017
Your Attention Is Required - NOW!
Virtually ALL my customers use
- Microsoft Security Essentials on Windows 7 and
- Windows Defender on Windows 8.x and Windows 10.
A really BAD bug has been uncovered that warrants your immediate attention.
Please follow the instructions in this article or alternatively you can do the following:
- Open Windows Defender (MS Security Essentials on Windows 7)
- Click on the Update tab
- No matter what the program says click on the big button Update Definitions
Stay safe.
Friday, May 5, 2017
"Security" software breaks Windows
It gets fun again - my life I mean; the rest of this blog post is dead serious, please make no mistake.
For years I have recommended NOT TO USE products from Webroot. I remember too many bad experiences with and infections on computers that were presumably "protected by Webroot".
In NBC's words:
An antivirus service used by tens of thousands of businesses and millions of home users shut down an untold number of computers around the world Monday after it mistakenly identified core parts of Microsoft Windows as threats, the company confirmed.Similar events have occurred in the past; sadly they are much more common than we would like and the public hardly knows about it. Some well known companies in the "computer security" or "anti virus" business have had similar snafus. Here is a quote from a blog post at Bleepingcomputer.com:
... Such mishaps have been reported for years to include major anti-virus/security vendors such as Panda, avast, AVG, BitDefender, Kaspersky, Malwarebytes, McAfee and Symantec. In most cases when these issues occur, the anti-virus vendors and security tool developers take quick action to correct the problem and provide support to those users who have been affected.To call such blunders a "mishap" is not a euphemism, IMHO it is outright glossing over or covering up a major blunder.
Things like this should not happen and they don't need to happen, they are major avoidable blunders. In every case we can only speculate about the "why" and I don't like to speculate.
What does all the above tell us? IMHO very simple:
Do not trust a single word in high gloss, pretty brochures.
Do not believe the words in computer related advertisements on TV.
Do not believe the words in computer related advertisements on TV.
What you find in high gloss publications is mostly marketing hype and likely not really trustworthy. And when certain "security" software seemingly out-of-the-blue suddenly is being hyped over the moon in TV advertisements it IMHO is time to run for the hills. It tells me that very likely a marketing campaign has to cover up some so called "mishap".
-----
So far I have used the acronym IMHO three times in this blog post. Generally there are always at least two ways to look at something, as we say around computers YMMV. If you have a different opinion - or maybe simply think I am a dumba.s then I ask you to please leave a comment, state your case or blow off steam below.
Thank you in advance.
Labels:
antivirus,
avast,
AVG,
Bitdefender,
Kaspersky,
Malwarebytes,
McAfee,
Norton,
security suite
Wednesday, April 26, 2017
Nothing New?
I got an email from a long time customer who asked me
... where have you been? Not on the Blog in three months...Here is my reply to him:
Thanks for checking the blog.And DO NOT click on links in emails! Check if the link goes to the correct web site! Rest your cursor on the link and look at the left bottom corner of the browser window; there you should see the text of the target URL ( = Internet address) that your browser will take you to if you click on that link. Learn to correctly read these URLs!
There is nothing new -- and that means no bad news and that is good news, right?
It still is the "old" story"; ransomware is at the top of the list of nasty programs.
The only way to avoid that junk fairly reliably - but not guaranteed - is NEVER to click on any attachment to any email!
Save the attachment to your desktop, upload the attachment to VirusTotal.com and have it checked there.
Even only one negative result is enough for me to tell the sender to check his attachments himself and stop sending out potentially infected junk files.
Stay safe!
Wednesday, January 25, 2017
WOT and the darned Purists at Mozilla
WOT vanished from many of my customers Firefox web browsers. I got some questions about that so here is my diatribe.
Mozilla, the maker of the Firefox web browser, is a European organization and over there they have a MUCH more narrow view of privacy issues. That is a double-edged sword.
WOT has a few month ago modified their end user license agreement to conform more closely to what the add-on all can do. No surprise to me that they collect some information on the things you search for and where you then click on. Google does that for years and nobody gives a hoot.
WOT finally made it public and Google and Mozilla went ballistic pulling the WOT extension (add-on) from their web sites. I am pretty livid but they don't listen to you or me.
WOT in the meantime has changed the wording of their end user license agreement and you again can get and run WOT in Goggle Chrome.
The Europeans don't seem to see the value of WOT for the normal non-geek end user and remain stubbornly on their negative stance towards WOT.
And Mozilla even tricks people into disabling or removing WOT - despite the fact that there is no even remotely similar functionality available anywhere else.
It is a shame but I have to tell my customers that they have to use Google Chrome for their web searches if they want the advantages of WOT, naturally with WOT and a good Ad-Blocker installed. These get installed from within the web browser, they are extensions.
Currently IMHO only Adblock Plus from adblockplus.org and uBlock Origin qualify as "good" ad-blockers.
Supposedly WOT and Mozilla are working on a resolution but that already takes many months.
If you have an affected computer and on the desktop is a folder named "Old Firefox Data" I may be able to resurrect WOT; but that definitely would be a trial and error thing that I can not guarantee. But at least I can do it remotely.
Stay safe.
Tuesday, January 24, 2017
Music Fans Take Note
Here is a quick tip for anyone who wants to build his/her own music library without over time paying a small fortune to Apple by using iTunes.
Please read this article on How-To Geek and get informed about alternatives to iTunes.
Stay safe.
Monday, January 9, 2017
How to stay safe in 2017 - Short List
Here is a short list of in my experience the most important steps you can take to keep your computer and your data safe. have I have added e few remarks for clarification.
- Update your software.
Not only Windows but all other regularly used programs as well;
for a Windows PC this includes (but is not limited to)
- Adobe Flash (beware of fake download sites!)
- Adobe Shockwave
- Web browser(s)
- Email client
- Java (if installed; mostly Java is not needed at all!)
- Office programs
We always have to keep in mind that some programs still don't update automatically and quietly in the background! Checking manually hardly ever has hurt anything.
- Back-up to an external hard drive.
Done regularly and correctly this currently is the only protection against ransomware viruses!
- Use a password manager.
For single machines see Keepass, for more than one machine see LastPass and include all cell phones and tablets in the count!
- Use a unique password for every account.
Everybody has many, many accounts; you need a password manager!
- Use random passwords
Easily done only with a password manager!
- Turn on two-step verification everywhere you can.
If you have a cell phone that you really use, otherwise this is pretty useless.
- Read and think(!) before you click.
"My" first commandment for safe computing.
- Enable full-disk encryption
On a single home computer? Only protects your data when the machine gets stolen.
- Put a six-digit PIN on your phone and set the phone to wipe it's contents if the PIN is guessed wrongly too many times.
Stay safe.
Labels:
browser,
encryption,
Flash Player,
general,
HowTo,
Java,
LibreOffice,
MS Office,
OpenOffice,
password,
ransomware,
recommended,
security
Sunday, January 1, 2017
Welcome 2017
A Happy, successful and healthy
NEW YEAR
to all my customers
and everybody else who might happen to read this!
Subscribe to:
Posts (Atom)