Just about a week ago an email conversation with an acquaintance and customer of mine went totally, horribly wrong. On first impulse I wanted to completely post the email exchange with my background thoughts added but all names except mine and all locations neutralized. My dear wife convinced me not to do that but rather try to explain why I asked the questions I asked. All this appears to be sufficiently important (to me at least!) to put it in a generalized form and to publish it here.
I need to write something that truthfully and forcefully makes it clear
beyond excuses, cop-outs and exceptions why I do request certain information. I have to get this across in a way that “hits home” with the vast majority of my customers; if I can't get this done I am going to burn out.
Here we go:
I receive many, many emails from customers with questions about technical issues and so far I believe not a single email has remained unanswered, either by an email reply or a phone call. And please consider that
my email advice is a free service!
Please remember,
I do not retain any personal information about my customers! No phone numbers, no address information and no information about their computer configuration. Why you ask? Simply because I need to avoid any risk of eventually being accused of “leaking” any of that to someone who is not entitled to this info and may misuse it.
From my side I see these emails with support questions as business communications, not personal ones. What I would expect in business communications is at least
proper identification and
contact info, that is
the sender's full name,
phone number and eventually address info. An example: A sending email address like risibisibear@isp.com signed with John is NOT correct identification. “risibisibear” does not resemble any name I know and I know at least twenty gentlemen named John.
And I ask to
please include that information in every email you send to me or I have to go on a wild goose chase, either scrolling and scrolling through a long
thread or even read through potentially many old emails from that customer to find that info. Frankly, I don't have the time to chase this sort of wild geese. If this info is missing most likely you will get a standard reply asking for the missing info.
As far as I know email is a fast and convenient way to send someone a
written note, aka a little letter. Do you like to get letters that miss addressing you with your name and/or missing a signature at the end? I didn't think so.
In this context I point you to one of the IMHO better web sites about
Netiquette (etiquette on the Internet), especially the
pages about email etiquette.
Every week I see many customers and I get many support questions via email. If I were to remember all technical and environmental details of all the many installations I have seen there wouldn’t be space left for anything else in my scatterbrain. And if I had to hunt down contact information every time I get a request from a customer there wouldn't be any time left to do actual customer visits.
Please include
technical info on what you are asking about; that includes all technical details, like what operating system you use, what program you are asking about, the version number and so on. Simply give as much detail as humanly possible if you want fast and good answers. These details can be (but are by no means limited to)
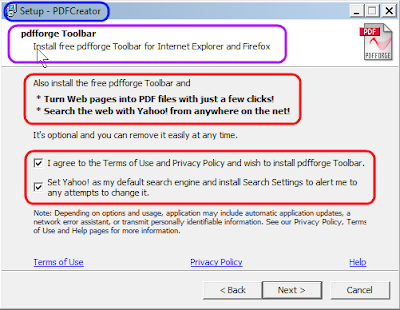
- a
screen shot instead of re-typing lengthy messages
- tell me what program you are using
- what you were attempting to do or achieve
- please spell names correctly
-
please use the reply button; this leaves the context in a longer conversation so I don't need to go on a wild goose chase to establish the context again
- if your question is about emails please tell me whether you “do” emails in a web browser and which one it is or in an email client like Thunderbird or Outlook.
Did you see my request to
please send a screen shot? If that seems too difficult please read
this article on my blog for more details; thank you.
Should you send your email from another than your own email account then please tell me so. I don't care for your reasons to do so but I do care about correctly addressing my reply!
PLEASE remember above explanations and understand that I need to
insist on everybody's cooperation. I do not want to get forced into a situation where I would have to charge for this service; that really is the last thing I want to do!
Lastly I want to quote two snippets of text from
this article on the NetManners blog:
"Simply because one is the “customer” certainly doesn’t give them permission to e-mail without any details, courtesy or proper e-mail etiquette."
"… when you e-mail with courtesy, details and clarity, you can bet the other side will value your business and go out of their way … to promptly answer your requests with the same! "
Am I asking too much? Frankly, I don’t think so.
As usual I welcome comments and suggestions right here in the blog. Thank you in advance.
Click here for a categorized Table Of Contents.