Wednesday, July 17, 2013
Is Government Data Collection Bad? (PRISM)
Just yesterday a customer asked me verbatim what I think "about all the fuss about the NSA having all our phone records".
I said that my personal opinion might be irrelevant because of my status in the country. And today I find this 10 minute video.
Be warned though: The speaker is a German stutterer with a strong accent. But what he says and visualizes made me shudder.
As usual I welcome suggestions and comments right here in the blog.
Click here for a categorized Table Of Contents.
Thursday, July 11, 2013
10 Commandments Of Safe Computing
- Thou shalt read and think(!) before you click.
- Thou shalt check for updates every week but ONLY on Windows 7/8!
- Thou shalt check Security Essentials (Win 7) or Defender (Win 8 & 10) every week.
- Thou shalt ask if thou knowest not.
- Thou shalt use only safe passwords.
- Thou shalt use common sense.
- Thou shalt not use Internet Explorer or MS Edge.
- Thou shalt not use any Microsoft email program/service.
- Thou shalt not use Bing for the bling.
- Thou shalt not visit pornographic websites.
As usual I welcome suggestions and comments right here in the blog.
Sunday, July 7, 2013
Gunk - Everyday Examples
On September 16, 2012 I wrote about a very bad example of a useful program trying to trick us into installing lots of unwanted software; admittedly this was an exceptionally bad example.
Last week I got my most beloved question about malicious and unwanted programs one too many times. It is the question "But how does this sort of program get on my computer? I certainly did not install it."
Here is my reaction to all this: Dear customer, you did it, I bet!
Let me show you some examples. Today I deliberately used the automatically appearing reminder to update Java; I used the mechanism that every unsuspecting computer user gets offered. The first program downloaded was a downloader which then in turn downloads the actual update.
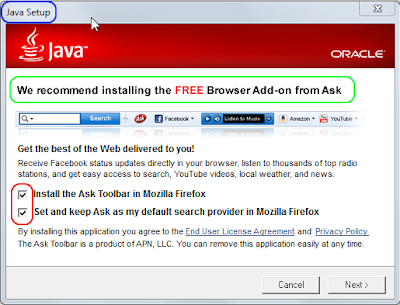
This and other "download" programs download not only the real updater program that you want and need, no, they almost always offer some unrelated software sort of disguised as part of the actual update, here Java. The installer for the Java update showed several common windows to select the location for the install, agree to the ubiquitous End User License Agreement and so on. And among all these small windows was this one:
The title shows clearly that Java Setup is running, see the blue marking. If you read the text in the window, and you should read it, you see that they, whoever that may be, "... recommends insrtalling the FREE Browser Add-on from Ask, see the green marking. And then it comes:
Two lines that very clearly state what the gunk software wants to do:
- Install the Ask Toolbar and
- "Set and Keep" Ask as the default search provider.
The "Set and Keep" is really tricky. Not only do they change your default search provider, they also tell the web browser not to allow future change.That means you can not just go in and set the browser back to the search provider of your choice.
Every single of my customers has heard me saying: Toolbars are POISON for computers, no exceptions and no matter whose name they carry, no matter where they come from, no matter who made them and no matter what they promise.
We have to read these little windows, see that there are pre-selected check marks and let our common sense tell us that the Ask Toolbar and Search Page have absolutely nothing to do with Java. We need to un-check both check marks or our web browser will be messed up - and then it will get worse and worse and in the end effect some of you will call me for help.
Update 2014-01-16:
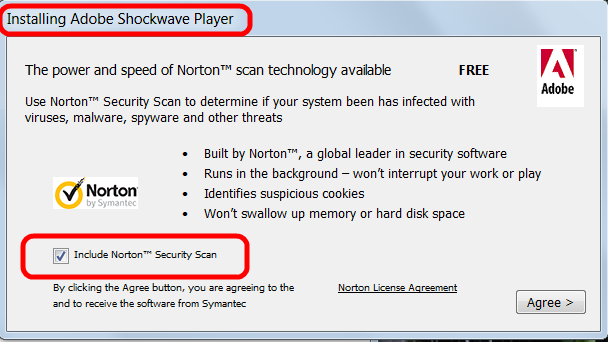
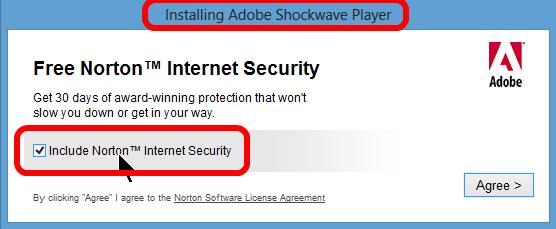
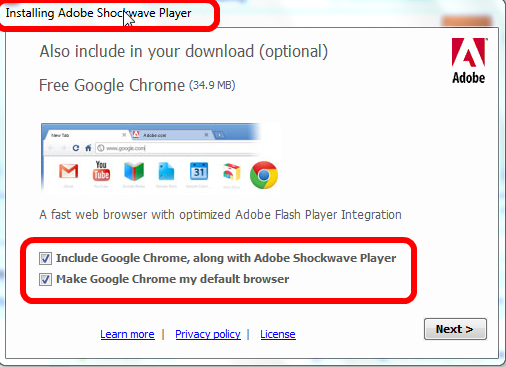
Here are more examples of the same process with different optics and different "gunk" to be foisted on our computers.
Updating Adobe Shockwave player would install Norton Security Scan.
Or, in different optics and different content because downloaded from a different download site:
IMHO the worst example because even Google employs these sneaky tactics:
This is how Google Chrome got on your computer Jerry G, you did allow it's installation.
Make no mistake, these things can happen with any installer or update of any program. Isn't it a shame that even well known big companies like Adobe, Oracle, Symantec (Norton products), McAfee and others employ these sneaky tactics trying to dupe us into installing something else than what we want?
Please save yourself the aggravation and some money, simply by paying attention!
As usual I welcome suggestions and comments right here in the blog.
Click here for a categorized Table Of Contents.
Subscribe to:
Posts (Atom)