I found an interesting article written by a Sophos product manager. The man is generally correct but I was amazed at the amount of what I perceive as spin. To save you the trouble of downloading the PDF file I quote the 10 myths here verbatim and will give you my opinion right after each paragraph – if applicable nad indented for readability.
Sophos is one of the better anti-virus and computer security companies geared squarely at the business market; just their ant-virus solution for a single computer is priced at $186.25 and thus of little interest to the vast majority of my customers.
Myth #1: The web is safe because I’ve never been infected by malware
You may not even know you’re infected. Many web malware attacks are designed to steal personal information and passwords or use your machine for distributing spam, malware or inappropriate content without your knowledge. For example, one Sophos customer recently installed a Web Appliance at its network gateway and immediately flagged more than 50 machines on its network for suspicious behaviour—calling home to a malware network for further instructions.
Myth #2: My users aren’t wasting time surfing inappropriate content
Without any kind of web filtering, you really have no idea what users are doing with their internet connection. The fact is that more than 40% of corporate internet use is inappropriate and going unchecked—an average of 1 to 2 hours per day per user. To make matters worse, the potential for employees being exposed to inappropriate content can have serious legal ramifications to any organization. The internet is full of studies related to internet use in the work place, from gambling and pornography to less nefarious activity such as social networking and travel planning. Furthermore, incidents of internet addiction disorder are increasing, with current estimates suggesting up to 5% to 10% of internet surfers have some form of web dependency.
The author speaks of “users” meaning employees in a company. But do you really know what family members and friends do when they use your computer?
Myth #3: We control web usage and our users can’t get around our policy
Anonymizing proxies make it easy for employees to circumvent your web filtering policy and visit any site they like. Anonymizing proxies are readily available and regularly exploited by school kids and employees alike. Hundreds of new anonymizing proxies are published daily to keep ahead of web security companies and resourceful users have even been known to setup their own private proxy at home to enable them to surf the web freely and unchecked. If you don’t think this is an issue, you can simply Google “bypass web filter” to see there are over 1.8 million ways to do this.
And even middle school kids often already know how to do this!Myth #4: Only porn, gambling, and other “dodgy” sites are dangerous
Hijacked trusted sites represent more than 83% of malware hosting sites. That’s correct. The majority of infected sites are websites that you trust and visit daily—they’ve just been hacked to distribute malware. Why? Because these sites are popular, high-traffic venues that silently distribute malware to unsuspecting visitors. Download the infected sites list to see just a small sampling of these kinds of sites.
Yes, 83% are trusted sites; it's gotten that bad. But don't go and try to find “the infected sites list”; I believe it does not exist. Should you find it please let me know!Myth #5: Only naive users get infected with malware and viruses
Malware from drive-by downloads happens automatically without any user action, other than visiting the site. Therefore, it doesn’t matter what level of computer expertise you have. The fact is, if you are visiting sites on the internet, you are at risk. The infected sites list provides just a small sampling of recently infected sites that distribute malware. If you visit sites like these, you are at risk.
FUD! (Fear, Uncertainty and Doubt). I can forgive him, he is a marketing manager.Myth #6: You can only get infected if you download files.
Most malware infections now occur through a “drive-by” download. Hackers inject the malicious code into the actual web page content, then it downloads and executes automatically within the browser as a by-product of simply viewing the web page. The malware is typically part of a professional exploit kit marketed and sold to hackers that leverages known exploits in the browser, operating system or plug-ins to infect the computer and download more malware. Again, it does all of this without a user having to do anything other than visit a hijacked web site. This graph shows the most popular exploit kits used in drive-by download attacks. Source: http://www.blade-defender.org/eval-lab/
Yes, he is basically correct.Myth #7: Firefox is more secure than Internet Explorer
But the graphics he links to are full of what I call spin; I strongly object to this.
If you are my customer or ever have listened to me on WTKM Radio you'll know how strongly I advocate to update, update and then update. To even test Internet Explorer 6 and 7 is in my opinion outright dishonest. Microsoft's main reasoning for creating new versions is improved security! Stay with an old version at your own risk.
And on top of it all we are not told what versions of Firefox 3 were used!
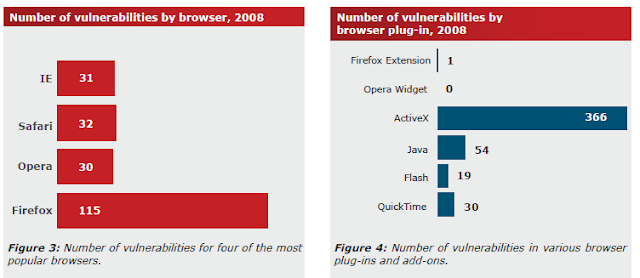
All browsers are equally at risk because all browsers are essentially an execution environment for JavaScript, which is the programming language of the web and therefore used by all malware authors to initiate an attack. In addition, many exploits leverage plug-ins such as Adobe Acrobat reader software, which runs across all browsers. Although the more popular browsers may get more publicity about un-patched exploits, it’s the unpublicized exploits you should be most concerned about. The fact is, there is no safe browser; when security research firm Secunia tabulated the number of browser exploits reported in 2008, Firefox was actually the least secure by a large margin:Source: http://secunia.com/gfx/Secunia2008Report.pdf
The gentleman IMHO is a true master of marketing spin. All this based on data from 2008; in the super fast world of computers that is age old! Please see the end of this article for more background on Firefox vs. IE relating to the source quoted here.Myth #8: When the lock icon appears in the browser, it’s secure.
The lock icon indicates there is an SSL encrypted connection between the browser and the server to protect the interception of personal sensitive information. It does not provide any security from malware. In fact, it’s the opposite because most web security products are completely blind to encrypted connections: it’s the perfect vehicle for malware to infiltrate a machine. Furthermore, some malware can exploit vulnerabilities to spoof SSL certificates to make users feel more secure or enable devious connections to fake banking sites. There are numerous recent examples of hackers creating elaborate phishing schemes that emulate bank, credit card, or PayPal sites complete with spoofed SSL certificates that are extremely difficult for the average user to identify as fraudulent. This is becoming an increasingly important security risk.
True; the lock icon only says that data transferred via the Internet is encrypted; this means your password and other data can not be understood by some crook passively listening to the Internet traffic with help of a sniffer or packet analyzer.Myth #9: Web security requires a trade-off between security and freedom
While the internet has become a mission critical tool for many job functions, whether it’s Facebook for HR or Twitter for PR, it’s completely unnecessary to create a trade-off between access and security. A suitable web security solution provides the freedom to grant access to sites that your users need while keeping your organization secure. Policy settings for groups or individuals don’t need to be complex—a few quick steps through a wizard are all a user needs to secure and enable your organization.
When evaluating a web security solution, be sure to focus on the administration tasks you will use most often, such as establishing special policies for users or groups. How easy are these tasks? How much time do they take? How many steps are involved? Is documentation required to navigate through the process? Ask these questions and more.
Good marketing, isn't it?Myth #10: Endpoint security solutions can’t protect against web threats
Typically, this has been the case because the web browser is essentially its own execution environment: It downloads content, renders it, and executes scripts all without any visibility outside the browser to endpoint security products. However, this is changing. As a result, it’s opening up a whole new approach to web security, particularly for mobile workers who are operating beyond the traditional boundaries of the corporate network. Be sure to check out the new Sophos Live Protection Web Filtering, which is part of our new Endpoint 9.5 security solution. Live Protection enables real-time malicious site filtering at the endpoint to protect mobile or remote workers who may be operating off the corporate network.
Now that we’ve busted several common myth’s and exposed the truth about web security risks, you’re probably thinking “Ok, how do I protect my organization and users?”. Good question. Fortunately, there’s a simple answer: Visit Sophos.com for more tips, tricks and more expert advice.
Now my comments.
So much for the scary world of myths. If you are still with me THANK YOU and congratulations for your determination.
Following myth #7 I promised to come back to the Firefox (FF) vs. Internet Explorer (IE) issue. For this purpose I have to insert a screen shot of the relevant part of the Secunia article the author quotes as his source.
Yes, in 2008 there were more reported vulnerabilities in Firefox than in IE. What they don't say is that the FF vulnerabilities were fixed very timely compared to Microsoft all too often taking weeks and months to fix IE – if at all. It seems worth noting here that my Secunia PSI still claims that IE8 has a non-fixable vulnerability!
And look at the number of ActiveX vulnerabilities; almost 4 times as many as all the others TOGETHER! And as my customers know, ActiveX needs IE to be able to run!
This makes it pretty clear to me that I seem to be on to something when I always say “Firefox is less insecure than IE”; even these old numbers show it!
To conclude this already way too long article here are three short quotes from this article:
- The probability of a user getting infected from a malvertisement [malicious advertisement] is twice as likely on a weekend and the average lifetime of a malvertisement is 7.3 days.
- 97% of Fortune 500 web sites are at a high risk of getting infected with malware due to external partners (such as JavaScript widget providers, ad networks, and/or packaged software providers).
- Fortune 500 web sites have such a high risk because 69% of them use external Javascript to render portions of their sites and 64% of them are running outdated web applications
And the publishers of this, here ZDNet as an example for all the others, are not giving us the names of the companies in question; IMHO a clear (but maybe unconscious) case of collusion.
As usual I welcome comments and suggestions right here in the blog. Thank you in advance.
Click here for a categorized Table Of Contents.

No comments:
Post a Comment